It was in the mid-July of 2015 when I had just completed compiling the financial report for the company that I work for as the fiscal year was approaching to an end and all the stakeholders were in high spirits to know how the company had fared in the previous twelve months. As my routine, I surfed through the internet and downloaded some of the comprehensive reports that had been published by other a few other companies for the purpose of comparison when the Hell broke loose. I had downloaded a malware with the documents that rendered almost all the programs in my PC dysfunctional. I lost all the data, the data that I had spent twelve months keenly preparing. Lucky enough, I had a backup storage that saved me the shame of negligence. The incidence prompted me to further look for ways to secure my cyber security, an initiative that has worked for me very efficiently.
Cybersecurity is the securing of computer systems against unauthorized cyber intruders who phish into these systems damaging either hardware or software mostly to steal information or to cause disruption in the case of misdirection of services. Cyber security is a wide task that includes the control of access to both computer hardware and protection against malware that maneuver their ways into the systems via code injection, data or network access. Cyber security is compromised when the operator(s) are tricked into deviations against secure procedures by the use of various hacking methods or when the operator intentionally follows this deviation. Ensuring safety has been an area of much interest in the recent past, and this has been brought about by an ever increasing use smart’ devices like smartphones and tablets that mostly use Wi-Fi and Bluetooth wireless networks and the internet in bringing their sophistications into perceived reality. The following are vulnerabilities and attacks that compromise the security of computers and other smart devices.
Backdoor
This is a commonly used method of hacking into systems done using a secret methodology that bypasses security controls and normal authentication. Poor configuration and original design are the ones exploited in this attack.
Denial of service Attack
As the term suggests, the attack is aimed at denying the access to services to its intended users. This is done by attackers deliberately entering wrong passwords consecutively beyond the allowed entry trials so as to prompt for the locking of target accounts. It can also be done through overloading the capabilities of a network or a computer system so as to deny access to all its users simultaneously.
Direct Access attack
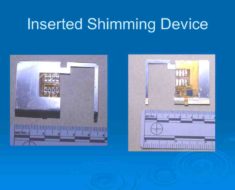
This is when a hacker physically accesses a computer system copying data to external devices or installing software keyloggers, worms and even using wireless mice.
Phishing
This technique is widely used to attack unsuspecting users who end up giving out their passwords, usernames and even credit card details carried out by instant messaging or spoofing.
Other methods used by hackers include Eavesdropping, Spoofing, Social engineering, Tampering, Privilege escalation and Clickjacking.
Rubica is an American digital security and privacy company found in San Francisco that offers the best solution in ensuring personal cyber security against ransomware.’ It is constituted of a team of experts who are globally recognized to provide robust and reliable digital security. Rubica’s team of elite cyber experts employ highly sophisticated techniques that typically operates in the background to guard on your online safety and alerting you whenever an action is required to be undertaken. Their efforts to secure the networks and machines have had 100% success rate, and it is for this reason I recommend them. Personally, my cyber security is managed by the company, and I can attest I have gotten value engaging them from the time I was hacked. The company has operated for more than a decade and has been hailed of its real-world experience in the protection of the most prominent persons in the world with personal cyber security. The cyber security experts of the company work from ops center based in the United States to monitor data of its clients and identify threats based on their behavioral patterns.
I know I am not the only one facing hacker threats as hundreds of thousand users of smart devices have their systems compromised every day in the global context. Reveton, CryptoLocker, CryptoWall, TorrentLocker, and Petya are among much other ransomware that Rubica experts have comprehensively managed to control. Every organization and people who care about the importance of safeguarding their data from intrusion have moved steadfastly to secure their systems with the help of Rubica experts. Ensuring my cyber security has been the most important thing since I was hacked as this has given me peace from external cyber-attacks. Using Rubica as personal cyber security can prevent these hacks and protect others from security hacks in the following ways. Rubica encourages you to back up important files and the system data, and it also suggest that you verify these backups regularly. This enables you to restore the files and system data in case the original verbatim data is lost through ransomware.
It always reminds you to exercise caution when surfing through sites like e-mail and opening their attachments. Zip and other compressed file attachments are the ones that mostly carry ransomware. It is advised to always contact them before even opening links sent to their computer for authentication. Rubica experts help its clients in updating operating systems and programs with the most current versions as to reduce vulnerability by hackers. Close attention to ULR is another factor that Rubica experts will always be available to help its prospective clients to ascertain. Some fake host site may appear identical to the legitimate ones, and for this reason, Rubica sorts this problem for its customers to seal all possible hacking loopholes. The company has come up with highly sophisticated cyber security protection that it helps its clients to install into their computer systems for protection. The experts provide services for the installation and maintenance of Firewalls and email filters to further guarantee their customers with comprehensive protection. Clients are also taught on how to secure their system with passwords so as to prevent hackers from accessing soft contents in case they physically access the systems. Therefore, Rubica is the best option for one who intends to shut hackers completely at once.
Dil Bole Oberoi